The deal with Apple's new AirTags
Not as powerful as GPS trackers, but more accessible to creeps
The NYTimes has a one-sided story on Apple’s AirTags, describing how creeps can stalk women or thieves can track target cars. I thought I’d write up some notes with more context.
An AirTag is not a GPS tracker. GPS trackers are small devices that communicate their position via 4G/5G mobile phone networks. They don’t use your phone, but communicate directly to the phone network. The devices cost about $40 and cost about $1/month for a low-bandwidth data plan. They are very popular in industry, as companies attach them to shipping containers, semi trailers, and other equipment. They are also popular for creeps stalking women. If you search for “GPS tracker” on Amazon.com, you’ll see that while they don’t come out and say this, it’s creepy men who they are primarily marketing to.
An AirTag is a BlueTooth tracker. BlueTooth supports a low-energy feature that allows devices with tiny batteries to operate continuously for a year, broadcasting a short message every minute. People attach these to their keychains, wallets, and purses to make them easy to find. You pick up the BlueTooth signal on your phone in order to locate the item the tracker is attached to — as long as the object is nearby, such as in your house. The major company that has been providing these devices is known as Tile; Apple just recently entered the market.
Apple’s innovation uses any nearby Apple device to forward these messages up to Apple. With Tile, you can largely only find the tagged object if your phone is nearby. With Apple AirTags, you can find the tracked object anywhere in the world — as long as somebody is nearby with an Apple iPhone. It doesn’t have a GPS, but instead, piggybacks on the GPS location of whatever phone it’s talking through. If you drop your keys on Berlin subway then fly home to Tokyo, you can still find your keys when somebody with an iPhone walks in range of them. This is a big deal. I put that in bold because the fact that all iPhones (and other Apple devices) are working together to track these tags is pretty darn fascinating.
Apple protects privacy with cryptography. AirTags have obvious privacy implications, both for tracking the AirTag itself as well as for the devices picking up broadcasts. Using clever crypto, Apple protects against the worst problems. Unfortunately, this means that Apple struggles to solve the creeper issue, because the necessary information to do so is hidden from them. Unlike most companies that profit by invading your privacy, Apple profits by protecting your privacy — they aren’t perfect, tradeoffs are hard, but they are sincere about it.
Creepers and thieves can obviously use AirTags the same way they’ve been using GPS trackers, even though they are technically different markets. A creeper boyfriend can hide one in his girlfriend’s purse. A guy at a bar can hide one under the bumper of a car of a target he met at a bar in order to follow her home. These are the sorts of stories the NYTimes describes above.
AirTags are no worse a threat than GPS trackers. The disappointing thing about the NYTimes story is that it only compares AirTags against other BlueTooth trackers like Tile, in which case, the potential for abuse by creepers is much worse. The NYTimes should’ve instead compared them against GPS trackers, which cost roughly the same and can be abused similarly. They aren’t identical, there are still tradeoffs, but stories dramatizing the creeper aspect do a disservice to the reader by pretending that AirTags are an outlier of technology when they are just part of the normal spectrum of trackers
We should still be concerned. Using GPS trackers requires advanced planning by a dedicated creep. In contrast, somebody could simply remove the AirTag from their keychain as a spur-of-the-moment decision in a bar and tape to a bumper in order to follow somebody home. But still, we should keep this in perspective — the world isn’t ending because Apple created the AirTag.
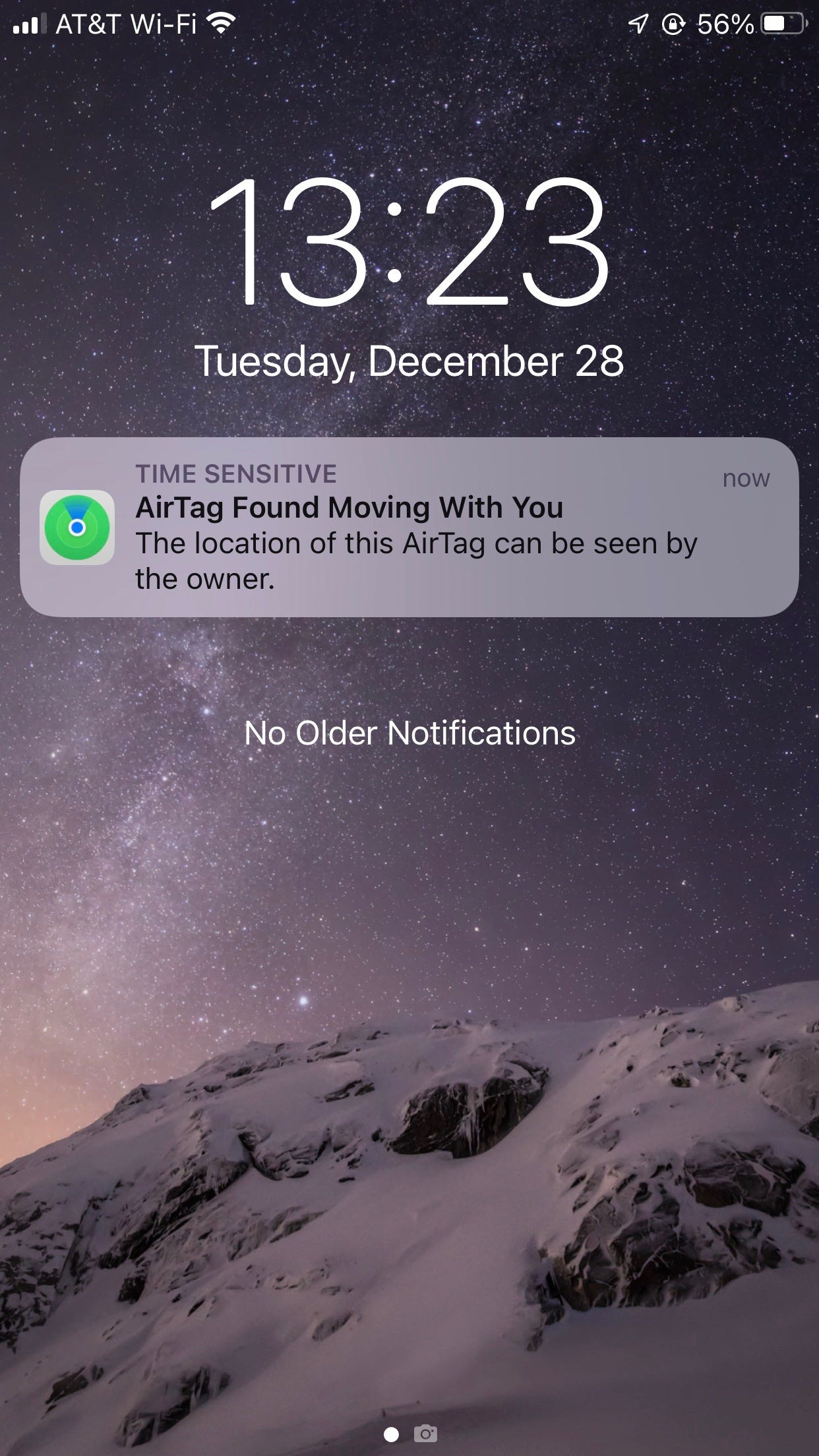
Apple tries to address the problem. If an AirTag, or other BlueTooth tracker, seems to be following you, then you iPhone will notify you are being tracked (see picture below). Any BlueTooth device not paired with your phone, but which seems to follow your phone, can be labeled suspicious. This can take several hours as you move from place-to-place for your phone to decide something suspicious is going on. The AirTag itself will also generate a warbling sound on its own, in case its paired phone is not around.
But Apple’s counter-measures have limitations. The AirTag changes its encrypted ID every 24 hours, so nearby phones can’t tell if the thing tracking you today is the same as what was tracking you yesterday. It also generates false-positives: carrying other BlueTooth devices not paired to your phone will cause your iPhone to give you a warning. Apple’s privacy-protecting crypto makes it hard from them to do better.\
We are bathed in BlueTooth broadcasts. It’s increasingly common for anything with electricity to have BlueTooth, and these things are constantly broadcasting little messages. Even something as simple as an at home Covid-19 test may have BlueTooth enabled. There are lots of fun creepy things you can do with them. For example, pay a few Uber drivers to drive around with burner phones for a month in order to pick up WiFi or BlueTooth broadcasts from a target, in order to locate their home address. The above NYTimes story is about what the least sophisticated stalker/thief can do with an AirTag, but there’s more interesting stories what sophisticated hackers can do.
I stalked my parents as an experiment. I told them I was experimenting on them, of course. I successfully tracked my parents to their house by hiding an AirTag in their car, but the garage blocked BlueTooth so they didn’t get warnings they were being tracked. I had my dad move the tracker into his pocket for better tracking, and a few hours later when he left the house to go to the store, he got a notification that he was being tracked. This shows that the anti-stalking features can work, but not perfectly. The picture below is the notification he got: