A serious definition of the unserious "zero-trust" buzzword
A saw a tweet that went something like this:
“I have 10 years of experience and several certifications, and I still don’t know what the heck ‘zero-trust’ is”
A lot of responses are sarcastic and humorous, so I thought I’d write up something sincere and serious, defining what this word actually means.
It’s an un-word
The word “Zero-Trust” isn’t really defined in terms of what it is, but what it isn’t.
It’s like the word “CISC” which only means “not RISC”. And yet, some people persist in trying to define the word “CISC” as if it really existed, as if there’s some “CISC” methodology or philosophy.
The same is true of “Zero-Trust”. The reason you can’t find a satisfying definition is because there isn’t any. What the word really means is “not the old cybersecurity practice”, namely that of a “perimeter firewall”. To understand it, you have to understand the previous cybersecurity practice that “Zero-Trust” rebels against.
What makes this particularly frustrating is how people try to formulate some principle out of the word “trust”. This is nonsense. What it originally meant was simply not trusting computers simply because they are inside the perimeter created by the firewall. Yet, people try to create some grander philosophy around the principle of “trust”.
This confuses everyone, because eventually, there’s always trust somewhere. “Zero” trust is not workable, even as an ideal. Once you authenticate and had your authorizations checked, you are trusted. There’s no version of “Zero-Trust” that leads to zero trust.
“Zero-Trust” is a slogan, a name. It’s like Oracle’s Unbreakable® trademark. This doesn’t mean their systems can’t be broken, it’s just a name. Similarly, “Zero-Trust” has nothing to do with “zero trust”.
When you see somebody try to create abstract principles about “trust” when defining the term, you know they are lying, simply making something up that won’t agree with anybody else’s definition.
The old practice
To define what “Zero-Trust” is, we have to define what it isn’t, the old standard cybersecurity practice of firewall perimeters and trusted internal networks.
In the 1970s, office networks were primarily dumb terminals connected to mainframes. in the 1980s, we had an explosion of “personal computers” on the desktop, networked together.
You didn’t even log into the first personal computers, you just sat down in front of them and started using them. Office networks were built on implicit trust that if you were in the building physically, then you could be trusted to operate the computer. You only “logged in” when accessing some distant computer on the network.
The Internet changed this. Suddenly your office computer was on a public network. The Morris Worm of 1988 showed how that was a problem.
The quick-and-dirty solution was the firewall. It largely isolated the “private” network from the “public” one.
This created a network with a hard shell on the outside, but a squishy inside. It was criticized from the beginning as not being real security. Whatever principles “Zero-Trust” embodies have always existed, from the mainframes of the 1960s to the cloud computing of today. There was just this brief time when companies took a shortcut with firewalls — but even then, they knew this was just a shortcut to true security.
At the same time, anti-virus products were popular in the 1990s. Everyone knew you had to buy firewalls and anti-virus for cybersecurity, and the rest was optional.
If you were selling any other product, you struggled to convince the mainstream market why they should buy it. This birthed a lot of buzzwords, like “defense in depth” and “layered security”, which simply mean that however much you are spending now, you to need spend more on an additional layer.
So many people seriously believe in such buzzwords. The original version of “defense in depth” was rational. It meant that if you were defending a castle or country, you would have a weak perimeter and a strong interior. If your army is stationed on the borders of your country, a surprise attack could wipe them out. Thus, you should move your army to the interior. An enemy would telegraph their true intentions crossing your border before they reached your army, giving them time to prepare.
For a castle, you have a fixed budget. If you put all that budget toward an impenetrable wall, it’ll get penetrated anyway. Instead, the strategy is to spend less on the wall and more on defenses in the interior. The wall would be weaker, yes, but the inner walls stronger.
These are otherwise sane principles, but not when applied to cybersecurity. You can’t argue making the perimeter weaker and applying that budget to the interior. Making anything weaker is impossible. You can only argue keeping spending on the perimeter the same, and then adding more budget to pay for extra layers in the interior.
The principle then becomes “spend more on security”, which of course, produces more security, and makes the non-firewall/non-antivirus vendors happy. There is no rational principle of rearrange a fixed budget, to spend less on the perimeter.
Thus, the majority of cybersecurity “principles” are simply slogans for why the budget must be increased. Vendors like it, empire builders within customers like it.
Analysts
Between the vendors and customers is a layer called “analysts” that try to interpret the needs of one into a language the other will understand. The best known analyst company is known as “Gartner” which pretends to rate which companies are the leaders/visionaries in their respective niches.
The thing about analysts is that they really don’t know how any of this works. When they judge a product (or service), they don’t look at the product itself. They instead look at the marketing literature and declare who has the best vision.
Among my career responsibilities has always been analyzing the competition, knowing how their products worked, being an expert in their products. This included being in the slightly grey area of reverse-engineering. Sure, I was frustrated that analysts didn’t understand my own product, but I was shocked at how little they understood those of my competitors as well. They evaluated marketing messages, not products.
It wasn’t completely messed up. They also talked to customers, asking them how the liked the product. But they usually talk to those on their level — managers, not techies. The managers are quite happy that they achieved the goals they bought the product for, but then you talk to the techies and they describe how they actually did their own thing to achieve those goals, and the product isn’t actually used.
The IT industry can be defined by this, the profound disconnect between the techies actually using the product and the views of management.
The upshot is that an enormous number of buzzwords are pushed by such analysts, if not outright invented by them. They are designed to help vendors communicate the value of their products to customers — especially those vendors selling things other than the traditional firewall/antivirus.
Zero-trust
In 2010, an analyst named John Kindervag working Forrester Research coined the term “zero-trust”. It meant the same thing as many other buzzwords: something to buy that wasn’t the traditional firewall/antivirus.
The technical definition is simply this:
[we] must eliminate the idea of a trusted network (usually the internal network) and an untrusted network (external networks) — [Forrester]
As I mentioned above, this idea wasn’t new. We’d been saying this from the moment firewalls were invented, that they are only a stopgap measure, that you shouldn’t have trusted internal networks.
But he put a word to what we’d all been saying, and that word somehow went viral.
It’s quite possible they were even commissioned to write the report by an anonymous vendor in order to market its products. A lot of analysts reports are written that way. A company hires an analyst to write a report about what they feel about a certain topic, and what the analyst writes happens to match the strategy of a specific company.
One big vendor started citing the Forrester report describing their product suite as “zero-trust”, and then, soon did all their competitors. That’s how product marketing works. Every company claims to do what the other companies do, but better. As soon as a big customer brings up the term “Zero-Trust” in a sales meeting, the sales person will say “Yes, we are a leader in zero-trust. We’ve got a good whitepaper on this. I’ll have our marketing guys send you a copy”. After the meeting, the sales person calls up marketing and asks “what the heck is zero-trust???”.
So within a few short years after Forrester coined the term, every company, and every cybersecurity product, was “Zero-Trust”. You won’t find a single cybersecurity product that isn’t an important part of a “Zero-Trust” architecture.
Some have tried to “precover” the term “Zero-Trust”. This is not a thing. The term was invented by Forrester to mean “not the perimeter firewall model”, and any previous use of those words means something else.
So what is it?
Given the negative definition “not the perimeter firewall model”, what is the positive description? What sorts of things can I definitely call “Zero-Trust”?
I’d suggest using the NIST definition as the starting point. They’ve expanded it a bit from the Forester definition to encompass BYOD:
Zero trust assumes there is no implicit trust granted to assets or user accounts based solely on their physical or network location (i.e., local area networks versus the internet) or based on asset ownership (enterprise or personally owned)
The NIST document is a pretty good discussion of modern security which could be improved by simply removing the word “Zero-Trust”.
I’d like the following as the three biggest points:
Microsegmentation and port isolation: Desktops are toxic, the thing we distrust the most. Desktops should be moved onto their network segments using “port isolation” so they can’t talk to each other, segmented from other things Similarly, other parts of the network should be segmented and controlled.
This doesn’t get the respect it deserves. My guess is because since it’s not a product a vendor will sell you, it’s not a strategy. Cybersecurity initiatives require funding, buy-in from management, careful planning. By definition, some IT person flipping a button on a switch enabling port isolation, without anybody noticing, is not a security initiative.
Remote, BYOD, and cloud: These things already broke your “firewall perimeter model”. This is especially true with the cloud — it’s they who have the trusted resources, it’s now you and your internal network they don’t trust. Note that remote VPN access that drops people on to the trusted interior network is an exceedingly bad design, but one people do a lot.
Identity, authorization, and authentication: These things have always existed, but have been hard to manage. Thus, we’ve made users admins over their own desktops and handed out admin rights willy nilly (such as to marketing execs who think they need the power).
Concepts like “least privileges” or “multi-factor authentication” are just features underneath these three categories.
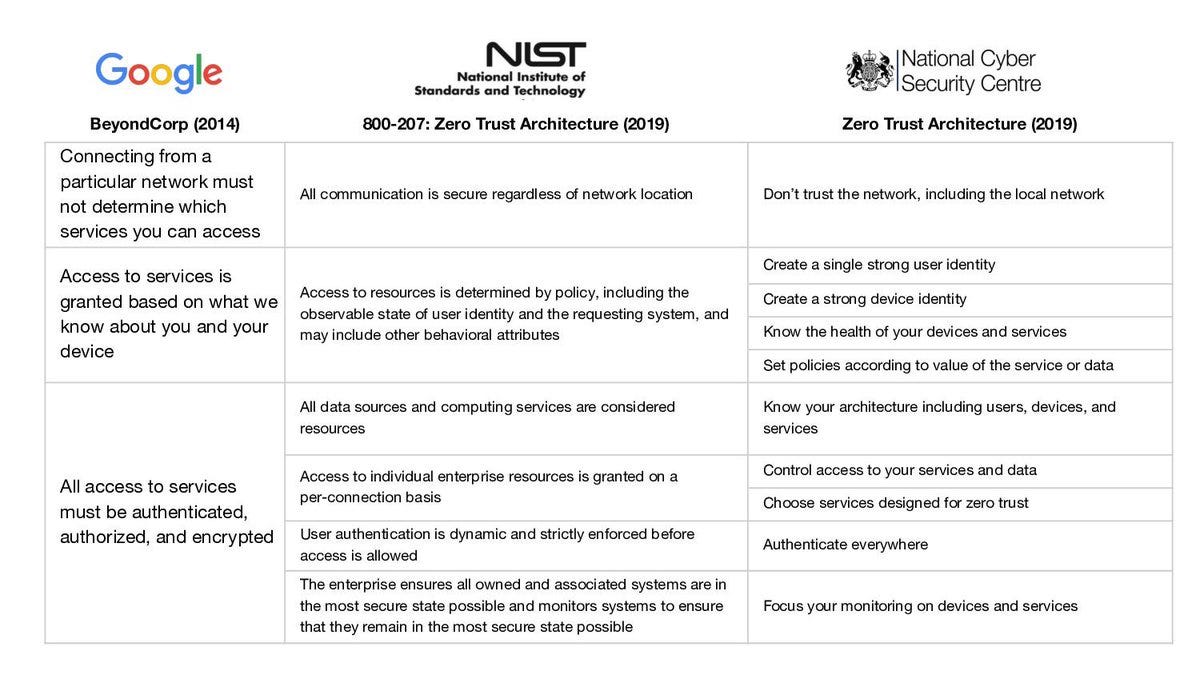
Along with NIST, there’s Google’s BeyondCorp and a British standard. I’d look to BeyondCorp as the standard you should follow. But I stress, all thee documents could be improved by not using the word “Zero-Trust”, and just thinking of them as “modern cybersecurity”.
So is it actually used?
Kinda.
Whatever you think your security architecture is, you have to cope with the cloud, BYOD, and remote workers. So everyone is doing some things. Passwords are a broken architecture, so multi-factor authentication is increasingly the standard. Some people call this part of “Zero-Trust”, but it’s something people do anyway.
Ransomware and nation-state actors exploit the trusted environment inside the firewall perimeter, so after a big hack, companies move to remove such trust, whether or not they say “Zero-Trust”.
At the same time, people still fall back to the perimeter firewall model. For example, CISA has a bunch of documents on how to resist ransomware and they all tell you to bolster your perimeter defenses. I can’t find a single CISA document that suggests what I think you need to do to combat ransomware: micro-segmentation, hierarchical domains, privileged workstations. Sure, they’ll hand-wave over “Zero-Trust”, but they won’t get into specifics.
Conclusion
The term “Zero-Trust” is a buzzword, a slogan. It has no real meaning, it’s not actually saying zero trust. It’s defined not by what it is, but by what it isn’t — it’s not the old model of a perimeter firewall and a trusted interior.
There is no cybersecurity today that isn’t “Zero-Trust” — including firewalls. Vendors quickly pivoted and made their firewalls a key component of the “Zero-Trust” strategy.
The term reflects the market, the way that customers depend upon vendors (and analysts) defining cybersecurity architectures, and vendors devising whatever marketing terms stick.
I’m not being cynical about vendors here. In fact, customers should pay attention more to vendors like Microsoft and Cisco, what their techies (rather than marketing/sales) say. Stop buying new products to solve your problems, learn better how to use the products you have.
But still, relying upon vendors to define your strategy is always going to be a bad idea. You’ll end up getting what sells best, not what works best.
Stop saying “Zero-Trust”. If you must, say “ZT” instead. The word “trust” has no particular meaning, no philosophy, no principle.
Update
As I posted this, I noticed this Dug Song tweet with this image contrasting three “Zero-Trust” standards. Dug Song founded a company that provided a real Zero-Trust product, that was wildly successful because customers liked it, because it worked and delivered on its promise. I’m not sure if Dug Song would agree with my description above, but whatever he says, you should trust him over me.
Solar Designer has a good reply to this tweet. (Again, listen to him, even if it disagrees with me). As I interpret his tweet, “Zero-Trust” sometimes becomes orthodoxy with Holy Crusaders fighting for the wrong things for the right reasons. For example, there’s the concept of “privileged workstations” that sit behind locked doors and not at home where your teenager installs malware — a thing we trust because of location.